Using Ollama to try a couple of models right now for an idea. I’ve tried to run Llama 3.2 and Qwen 2.5 3b, both of which fits my 3050 6G’s VRAM. I’ve also tried for fun to use Qwen 2.5 32b, which fits in my RAM (I’ve got 128G) but it was only able to reply a couple of tokens per second, thereby making it very much a non-interactive experience. Will need to explore the response time piece a bit further to see if there are ways I can lean on larger models with longer delays still.
chiisana
- 2 Posts
- 402 Comments

 3·19 days ago
3·19 days agoNeither ignorance towards, nor or malice against, the people they’re supposed to represent should be permitted. Politicians should only ever argue policies against the policies’ merits, and not antagonize the people the policies affect.

 161·23 days ago
161·23 days agoIt was never to your definition of free, so you were never going to be using it in the first place. Don’t need to say goodbye when you were never here.

 22·23 days ago
22·23 days agoIf you’re going to use it, you’d be paying for it one way or another; either through money or privacy. Par for the course.

 313·1 month ago
313·1 month agoRemoved by mod

 1875·2 months ago
1875·2 months agoiOS supports VPN out of the gate. Apps just make it easier to configure. Please don’t spew divisive misinformation, regardless if this is ignorant to the facts or otherwise.
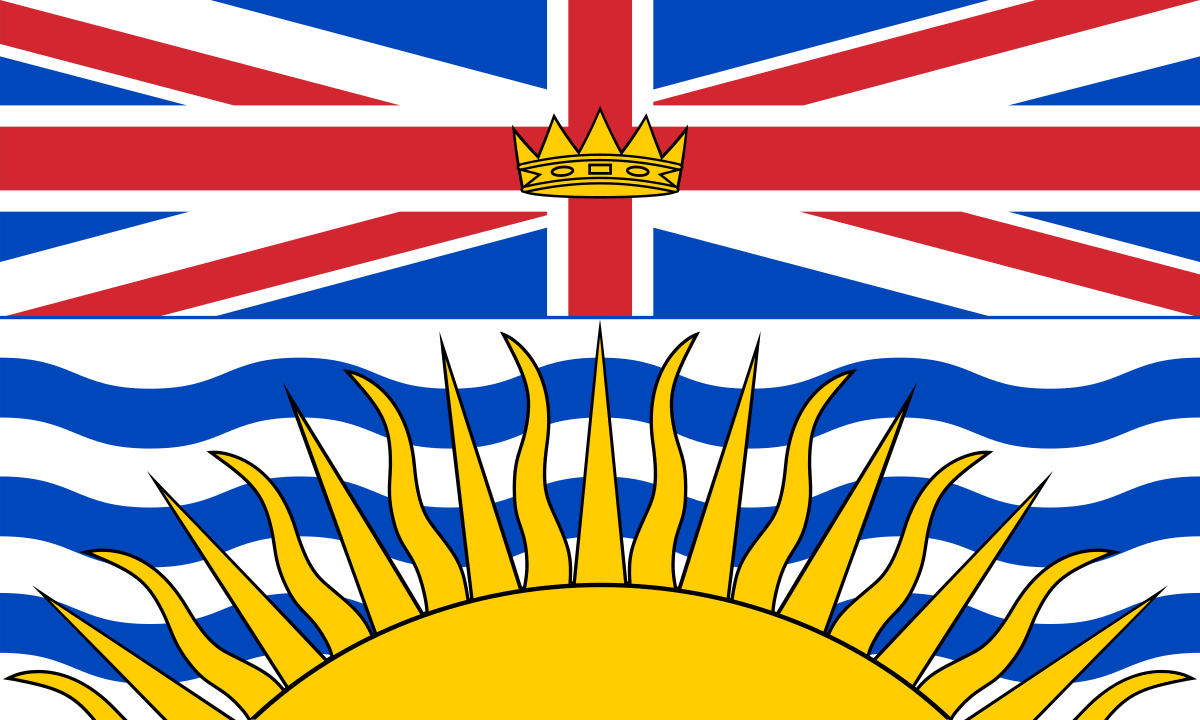
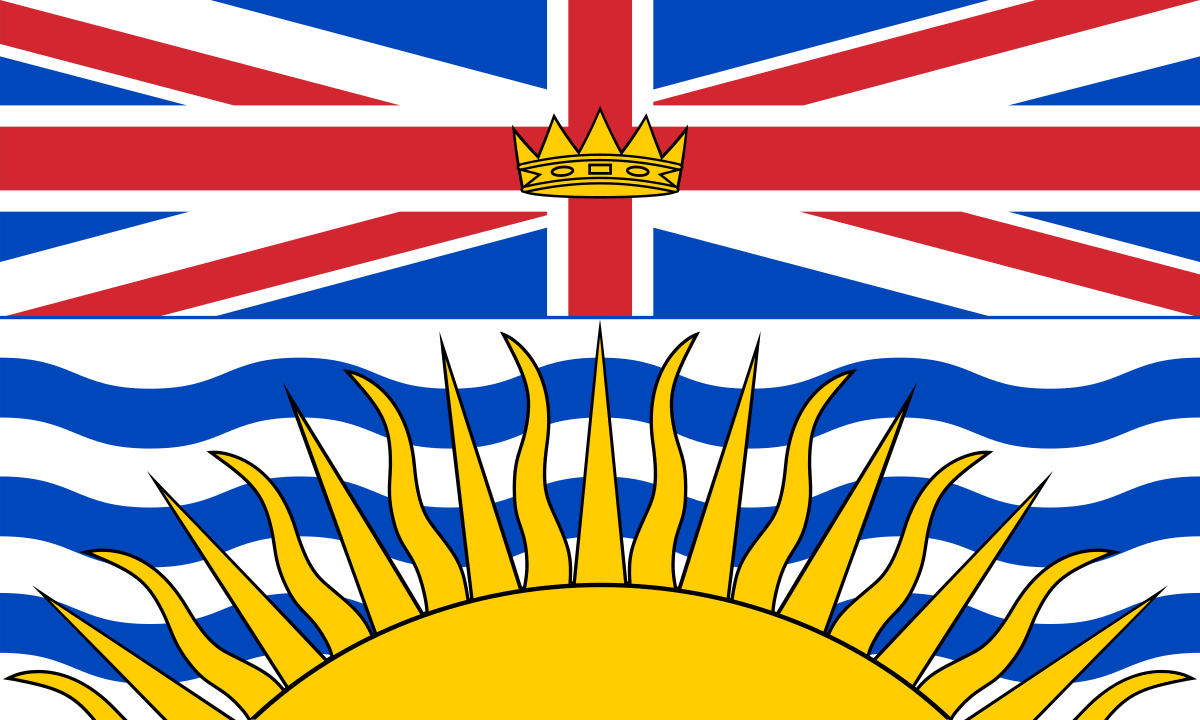
Don’t forget to register and go out to vote people! This looks closer than ever :(

 12·2 months ago
12·2 months agoThis is Apple; they value different things than most people… sometimes warranted, results in offering a much better experience, and pushes everything forward (see MagSafe -> Qi2 for recent example), other times they’re just regarded as late adopters. The detraction of visual aesthetics from folding crease is apparently one of such things that they care about.
Amazing stuff. Thank you so much!

 1·2 months ago
1·2 months agoThe LM password hash (predecessor to NTLM) was calculated in two blocks of 7 characters from that truncated 14 characters. Which meant the rainbow table for that is much smaller than necessary and if your password is not 14 characters, then technically part of the hash is much easier to brute force, because the other missing characters are just padded with null.

 1·2 months ago
1·2 months agoIf memory serves, 175B parameters is for the GPT3 model, not even the 3.5 model that caught the world by surprise; and they have not disclosed parameter space for GPT4, 4o, and o1 yet. If memory also serves, 3 was primarily English, and had only a relatively small set of words (I think 50K or something to that effect) it was considering as next token candidates. Now that it is able to work in multiple languages and multi modal, the parameter space must be much much larger.
The amount of things it can do now is incredible, but our perceived incremental improvements on LLM will probably slow down (due to the pace fitting to the predicted lines in log space)… until the next big thing (neural nets > expert systems > deep learning > LLM > ???). Such an exciting time we’re in!
Edit: found it. Roughly 50K tokens for input output embedding, in GPT3. 3Blue1Brown has a really good explanation here for anyone interested: https://youtu.be/wjZofJX0v4M

 24·2 months ago
24·2 months agoThe models are not wrong. The models are nothing but a statistical model that’s really good at predicting the next word that is likely to follow base on prior information given. It doesn’t have understanding of the context of the words, just that statistically they’re likely to follow. As such, all LLM outputs are correct to their design.
The users’ assumption/expectation of the output being factual is what is wrong. Hallucination is a fancy word in attempt make the users not feel as upset when the output passage doesn’t match their assumption/expectation.

 61·2 months ago
61·2 months agoThe network effect is too strong. The minority that are whining here isn’t going to make a dent. Next time you’re out, look at how many people are using ads ridden apps instead of paying $0.99 or whatever to remove them. The users have already decided their time and privacy is worthless and would rather getting the service for “free”.

 1·2 months ago
1·2 months agodeleted by creator

 5·2 months ago
5·2 months ago4o does perform web searches, give summaries from a couple of pages, and include the link to those pages when prompted properly.
However, as most people know, first couple results doesn’t always tell the full picture and further actual researches are required… but, most “AI assistant” (also including things like those voice assistants in speakers) users tends to take the first response as fact…
¯\_(ツ)_/¯

 10·2 months ago
10·2 months agoReducing ad spend on one platform, albeit often the elephant in the room for most companies’ online marketing department, isn’t going to reduce prices at the till. Companies will either reallocate the ad spend elsewhere, there by spamming more ads in front of everyone, or pocket the difference to pad their profit margin.

 21·2 months ago
21·2 months agoGoogle did not make RCS; RCS is made by GSM consortium as succession of SMS, Google extended it to add some extra features such as end to end encryption (but only when messages are routed through their servers).
China mandated 5G sold in China must support RCS, hence why Apple added support for this. Since Google is basically banned in China, you can pretty much bet RCS going into/out of China is going to be unencrypted.
So you’re basically stuck between getting inferior unencrypted messages, or routing everything through Google.
Avoid RCS like the plague.

 9·2 months ago
9·2 months agoIt is easier to think of the SSL termination in legs.
- Client to Cloudflare; if you’re behind orange cloud, you get this for free, don’t turn orange cloud off unless you want to have direct exposure.
- Cloudflare to your sever; use their origin cert, this is easiest and secure. You can even get one made specific so your subdomains, or wildcard of your subdomain. Unless you have specific compliance needs, you shouldn’t need to turn this off, and you don’t need to roll your own cert.
- Your reverse proxy to your apps; honestly, it’s already on your machine, you can do self signed cert if it really bothers you, but at the end of the day, probably not worth the hassle.
If, however, you want to directly expose your service without orange cloud (running a game server on the same subdomain for example), then you’d disable the orange cloud and do Let’s Encrypt or deploy your own certificate on your reverse proxy.

 1·2 months ago
1·2 months agoI don’t think it is a “problem”, but it gets really boring / bleak when every single house looks identical to one another.
Also, I’m still more inclined to introduce additional townhouses as well as low / mid rises to increase the density, as opposed to these detached designs.
The amount of confidently incorrect responses is exactly what one could expect from Lemmy.
First: TCP and UDP can listen on the same port, DNS is a great example of such. You’d generally need it to be part of the same process as ports are generally bound to the same process, but more on this later.
Second: Minecraft and website are both using TCP. TCP is part of layer 4, transport; whereas HTTP(S) / Minecraft are part of layer 7, application. If you really want to, you could cram HTTP(S) over UDP (technically, QUIC/HTTP3 does this), and if you absolutely want to, with updates to the protocol itself, and some server client edits you can cram Minecraft over UDP, too. People need to brush up on their OSI layers before making bold claims.
Third: The web server and the Minecraft server are not running on the same machine. For something that scale, both services are served from a cluster focused only on what they’re serving.
Finally: Hypixel use reverse proxy to sit between the user and their actual server. Specifically, they are most likely using Cloudflare Spectrum to proxy their traffic. User request reaches a point of presence, a reverse proxy service is listening on the applicable ports (443/25565) + protocol (HTTPS/Minecraft), and then depending on traffic type, and rules, the request gets routed to the actual server behind the scenes. There are speculations of them no longer using Cloudflare, but I don’t believe this is the case. If you dig their mc.hypixel.net domain, you get a bunch of direct assigned IP addresses, but if you tried to trace it from multiple locations, you’d all end up going through Cloudflare infrastructure. It is highly likely that they’re still leaning on Cloudflare for this service, with a BYOIP arrangement to reduce risk of DDOS addressed towards them overflow to other customers.
In no uncertain terms:
mc.hypixel.net, but also have a SRV record for_minecraft._tcp.hypixel.netset for 25565 onmc.hypixel.netmc.hypixel.netdomain has CNAME record formt.mc.production.hypixel.io.which is flattened to a bunch of their own direct assigned IP addresses.